华为USG6000:NAT与NAT Server设置案例
华为防火墙USG6000:NAT和NAT Server配置案例
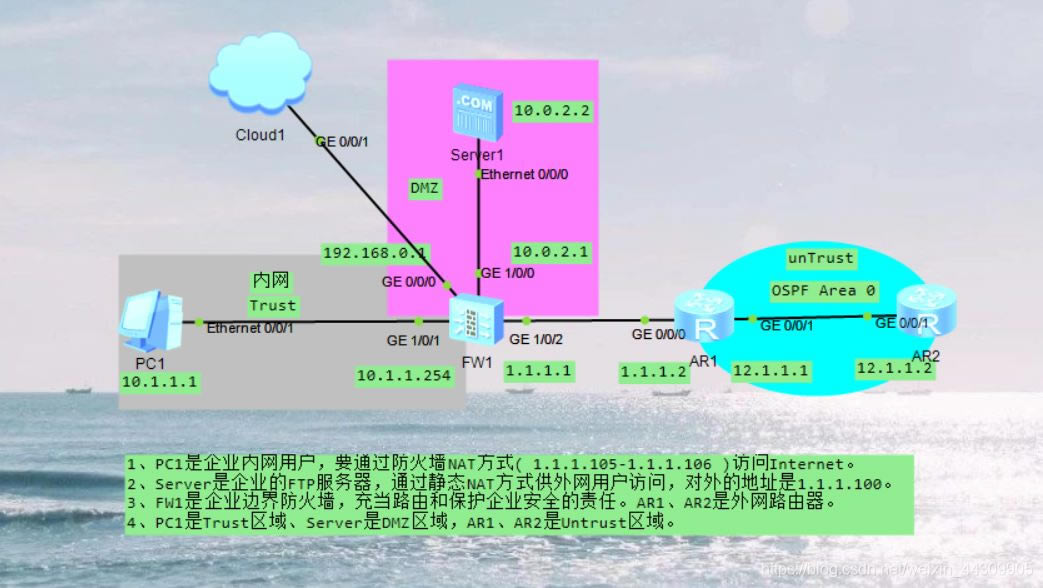
- 网络拓扑图
- 通过WEB方式登录到防火墙
- 登录成功
- 配置防火墙使内网用户通过PAT方式上网
- 配置防火墙使得外网用户能访问企业DMZ区域的FTP服务器(双向nat)
- 内网用户与FTP-Server配置
- 配置代码
- 官方参考文档
网络拓扑图
通过WEB方式登录到防火墙
通过Web方式登录USG6000V:教程

登录成功

配置防火墙使内网用户通过PAT方式上网
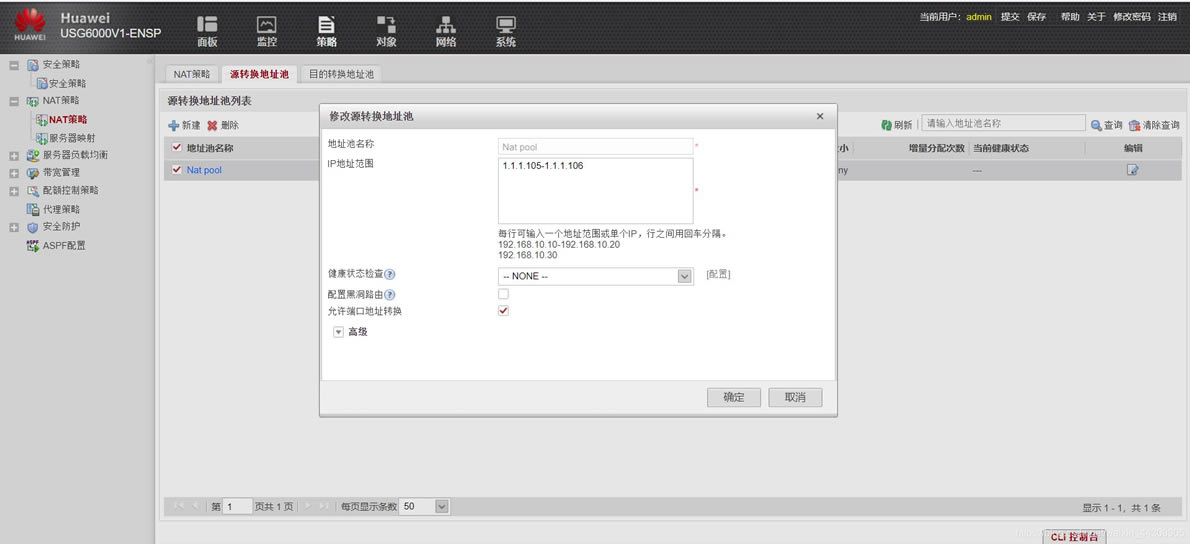
防火墙上新建一个Nat Pool,供内网用户以NAT方式访问外网
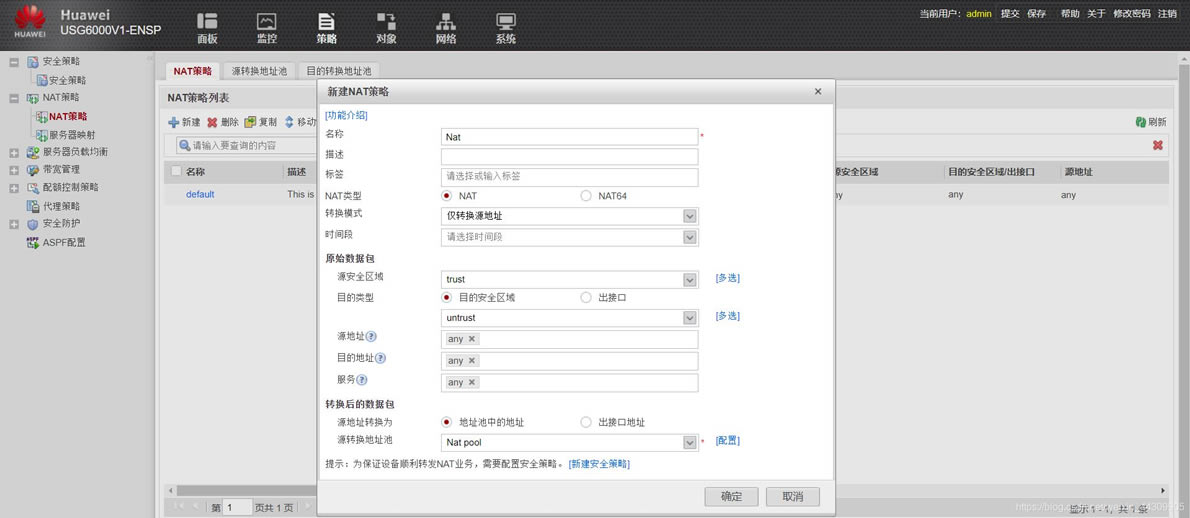
配置Nat策略
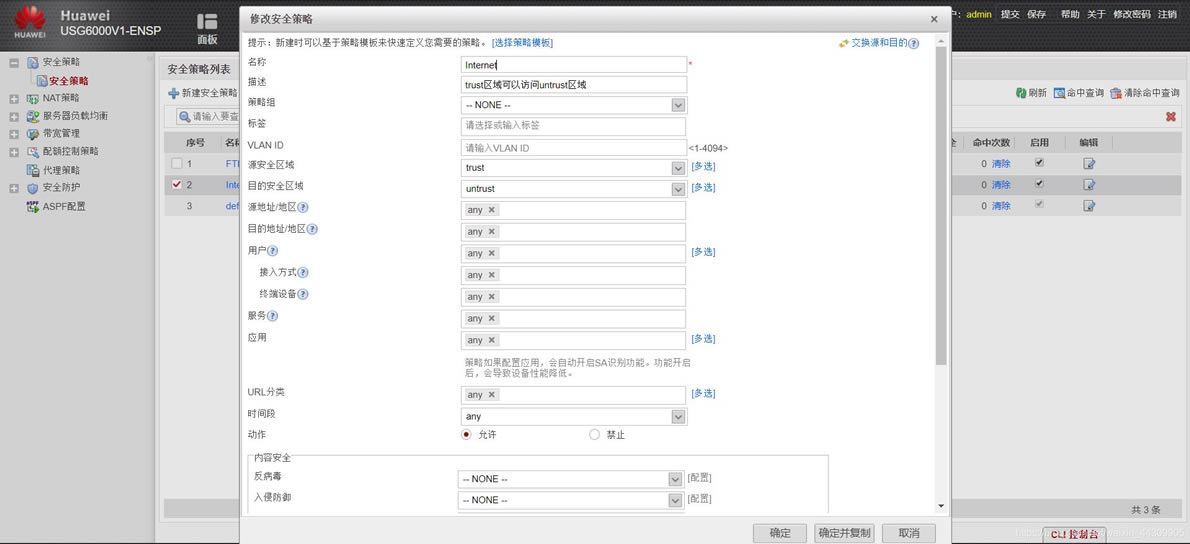
配置策略,使得trust区域可以访问untrust区域
配置默认路由,指向R1
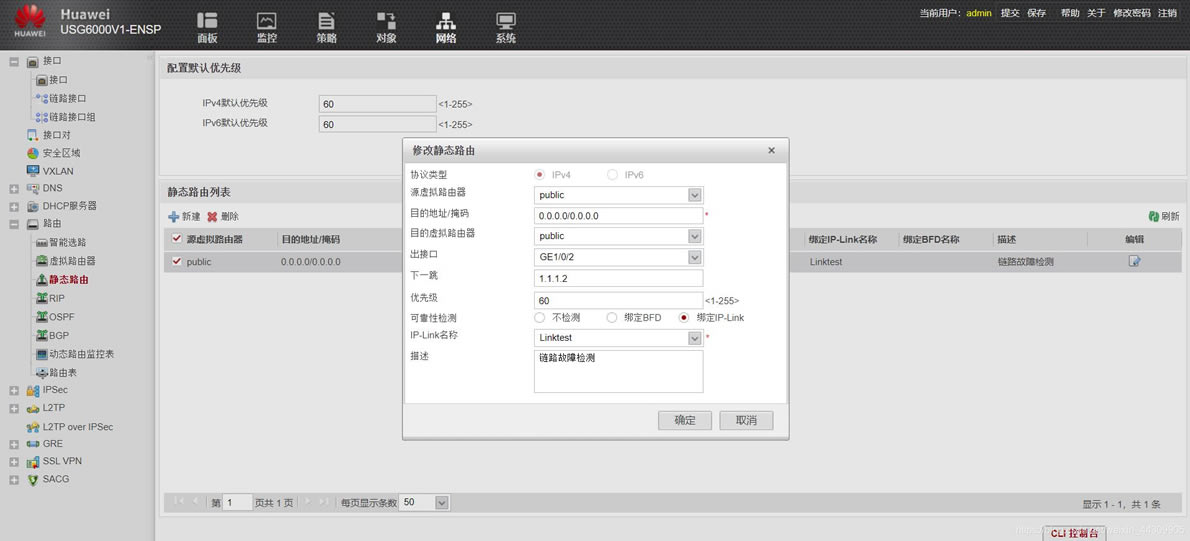
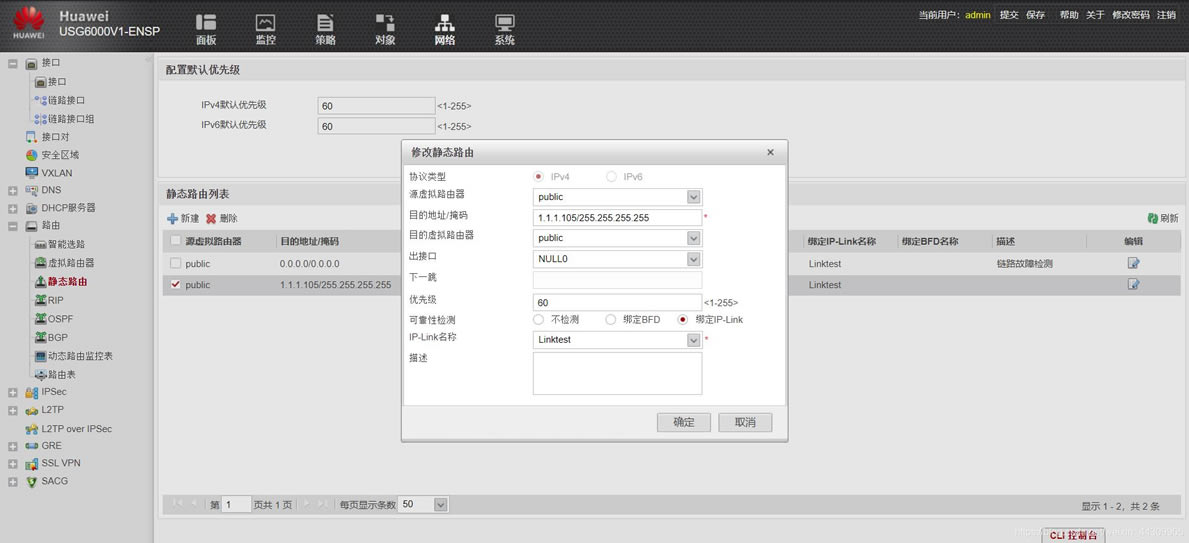
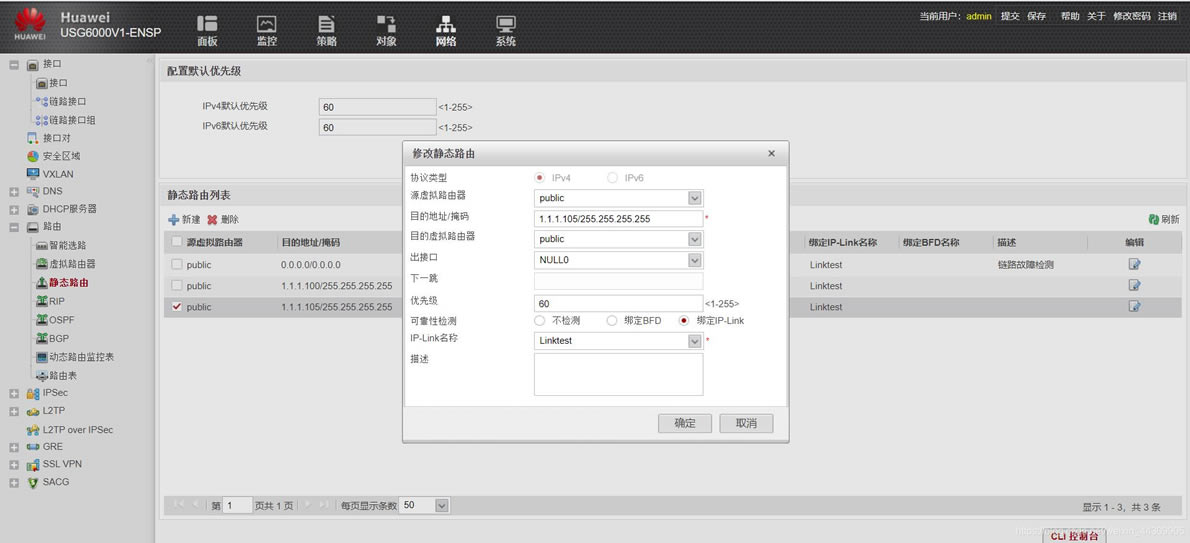
设置到达Nat Pool的静态路由,指向一个空接口,防止路由黑洞
配置防火墙使得外网用户能访问企业DMZ区域的FTP服务器(双向nat)
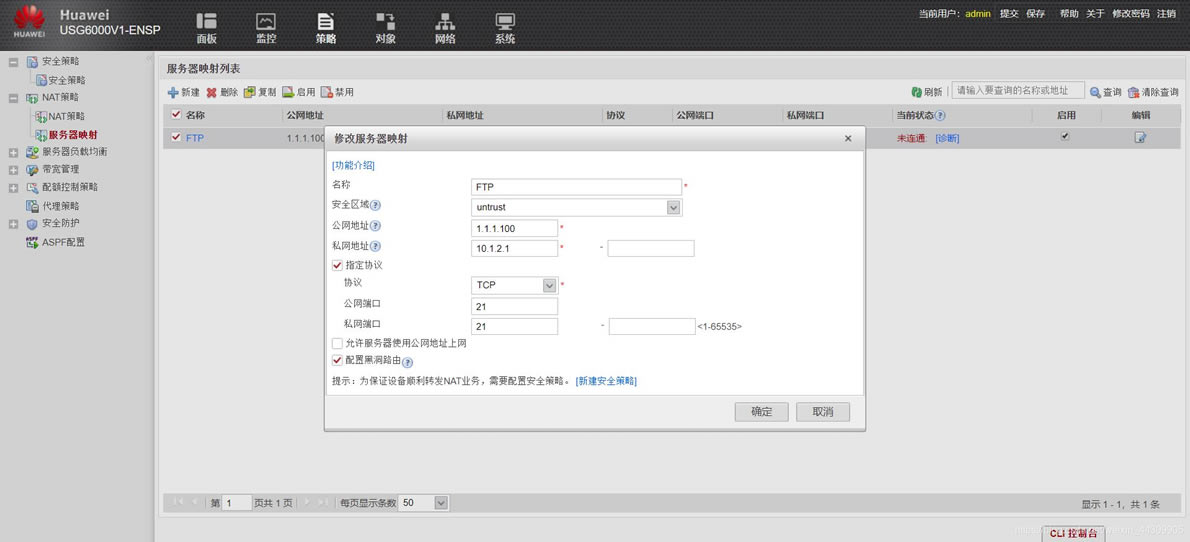
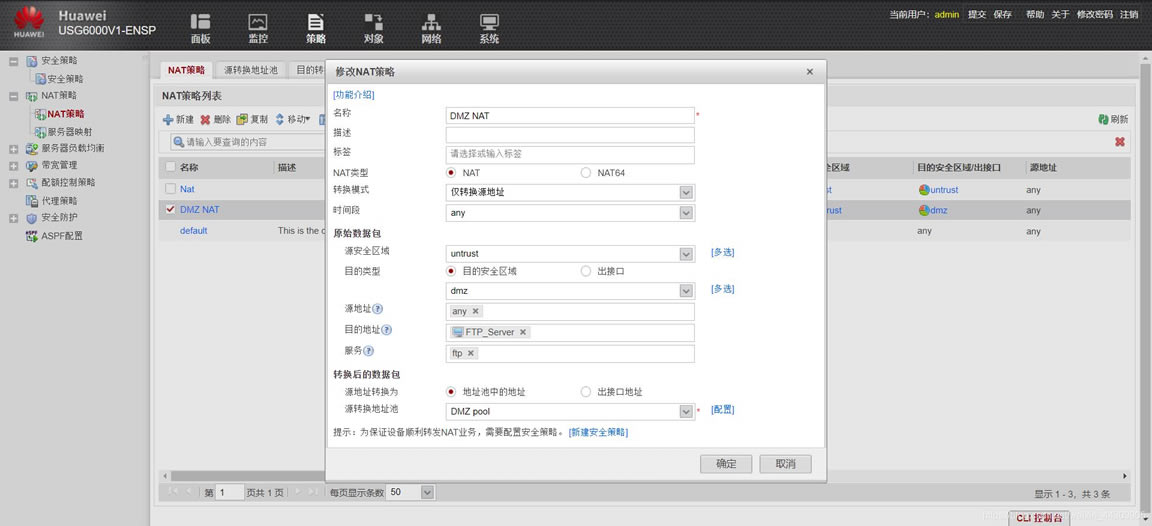
先配置服务器对外静态映射
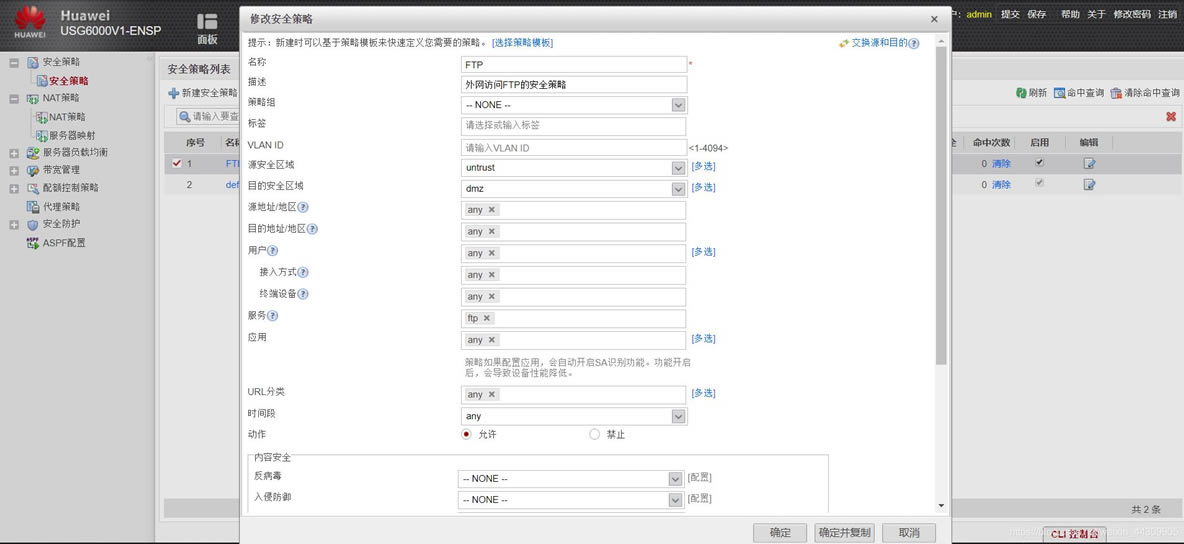
防火墙上配置一个策略,使得untrust区域能访问DMZ区域
配置nat pool地址池,目的是作为外网用户访问内网服务器后nat的内网地址
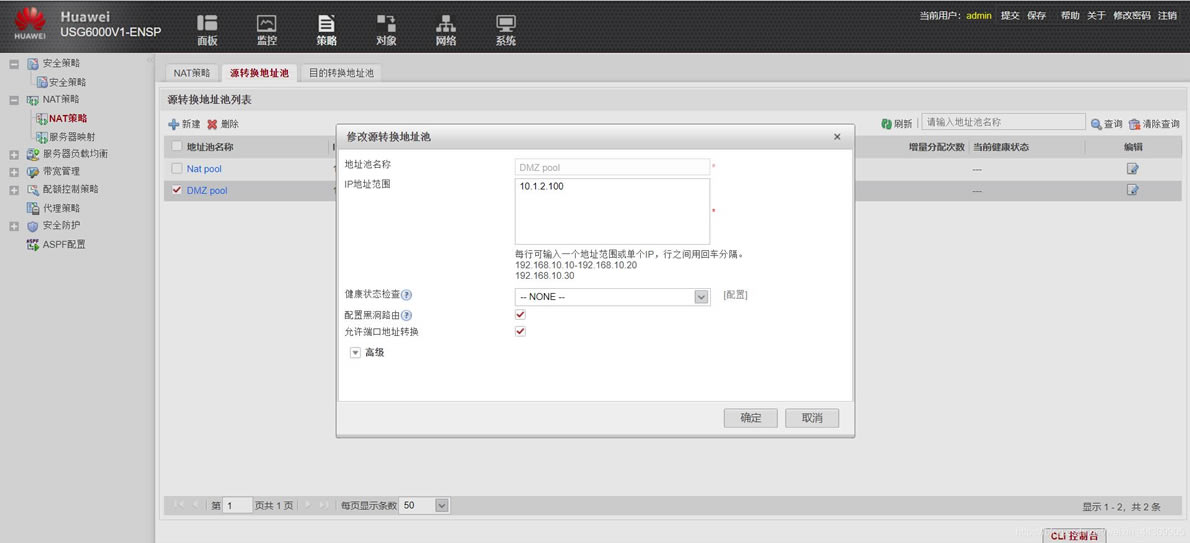
配置一个nat策略。注意,这个nat策略和内网nat外网有所不同!!!
最后配置一个到达服务器对外地址的静态路由,防止路由黑洞
WEB界面配置完成
内网用户与FTP-Server配置
- PC1
- FTP-Server
配置代码
- FW
dis current-configuration 显示防火墙的运行配置
1
[USG6000V1]dis current-configuration
2020-12-02 05:10:12.380
!Software Version V500R005C10SPC300
#
sysname FW
l2tp domain suffix-separator @
#
ipsec sha2 compatible enable
#
undo telnet server enable
undo telnet ipv6 server enable
#
update schedule location-sdb weekly Sun 04:29
#
firewall defend action discard
#
banner enable
#
user-manage web-authentication security port 8887
undo privacy-statement english
undo privacy-statement chinese
page-setting
user-manage security version tlsv1.1 tlsv1.2
password-policy
level high
user-manage single-sign-on ad
user-manage single-sign-on tsm
user-manage single-sign-on radius
user-manage auto-sync online-user
#
web-manager security version tlsv1.1 tlsv1.2
web-manager enable
web-manager security enable
#
firewall dataplane to manageplane application-apperceive default-action drop
#
undo ips log merge enable
#
decoding uri-cache disable
#
feedback type threat-log enable
feedback type pdns enable
#
update schedule ips-sdb daily 01:03
update schedule av-sdb daily 01:03
update schedule sa-sdb daily 01:03
update schedule cnc daily 01:03
update schedule file-reputation daily 01:03
#
ip vpn-instance default
ipv4-family
#
ip-link check enable
ip-link name Linktest vpn-instance default
destination 0.0.0.0/0.0.0.0 interface GigabitEthernet0/0/0 mode icmp next-hop 1
.1.1.2
#
ip address-set FTP_Server type object
address 0 10.1.2.100 mask 32
#
time-range worktime
period-range 08:00:00 to 18:00:00 working-day
#
ike proposal default
encryption-algorithm aes-256 aes-192 aes-128
dh group14
authentication-algorithm sha2-512 sha2-384 sha2-256
authentication-method pre-share
integrity-algorithm hmac-sha2-256
prf hmac-sha2-256
#
aaa
authentication-scheme default
authentication-scheme admin_local
authentication-scheme admin_radius_local
authentication-scheme admin_hwtacacs_local
authentication-scheme admin_ad_local
authentication-scheme admin_ldap_local
authentication-scheme admin_radius
authentication-scheme admin_hwtacacs
authentication-scheme admin_ad
authorization-scheme default
accounting-scheme default
domain default
service-type internetaccess ssl-vpn l2tp ike
internet-access mode password
reference user current-domain
manager-user audit-admin
password cipher @%@%Zrwy:l}UIX`r(g+IY`OVqb^q${UL$9Sr[@{C_yFj6fV)b^tq@%@%
service-type web terminal
level 15
manager-user api-admin
password cipher @%@%RbIt"(浏览器部落,专业提供软件下载)
>Pz2NW1b@+[5@*lAb@{Q@w,<><\:fm\\"=admhabcl@%@% level="" 15="" manager-user="" admin="" password="" cipher="" @%@%="" #t."\i!cn:fcall.sly9e%="">]n*,Vrv~4DZU.{&N6r8:e%A9@%@%
service-type web terminal
level 15
role system-admin
role device-admin
role device-admin(monitor)
role audit-admin
bind manager-user audit-admin role audit-admin
bind manager-user admin role system-admin
#
l2tp-group default-lns
#
interface GigabitEthernet0/0/0
undo shutdown
ip binding vpn-instance default
ip address 192.168.0.1 255.255.255.0
alias GE0/METH
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage snmp permit
service-manage telnet permit
interface Virtual-if0
#
interface NULL0
#
firewall zone local
set priority 100
#
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
#
firewall zone untrust
set priority 5
#
firewall zone dmz
set priority 50
#
ip route-static 0.0.0.0 0.0.0.0 GigabitEthernet1/0/2 1.1.1.2 track ip-link Linkt
est description 链路故障检测
ip route-static 1.1.1.100 255.255.255.255 NULL0 track ip-link Linktest
ip route-static 1.1.1.105 255.255.255.255 NULL0 track ip-link Linktest
#
undo ssh server compatible-ssh1x enable
ssh authentication-type default password
ssh server cipher aes256_ctr aes128_ctr
ssh server hmac sha2_256 sha1
ssh client cipher aes256_ctr aes128_ctr
ssh client hmac sha2_256 sha1
#
firewall detect ftp
#
nat server FTP zone untrust protocol tcp global 1.1.1.100 ftp inside 10.1.2.1 f
tp no-reverse unr-route
#
user-interface con 0
authentication-mode aaa
user-interface vty 0 4
authentication-mode aaa
protocol inbound ssh
user-interface vty 16 20
#
pki realm default
#
sa
#
location
#
nat address-group "Nat pool" 0
mode pat
section 0 1.1.1.105 1.1.1.106
#
nat address-group "DMZ pool" 1
mode pat
route enable
section 0 10.1.2.100 10.1.2.100
#
multi-linkif
mode proportion-of-weight
#
right-manager server-group
#
device-classification
device-group pc
device-group mobile-terminal
device-group undefined-group
#
user-manage server-sync tsm
#
security-policy
rule name FTP
description 外网访问FTP的安全策略
source-zone untrust
destination-zone dmz
service ftp
action permit
#
auth-policy
#
traffic-policy
#
policy-based-route
#
nat-policy
rule name Nat
source-zone trust
destination-zone untrust
action source-nat address-group "Nat pool"
rule name "DMZ NAT"
source-zone untrust
destination-zone dmz
destination-address address-set FTP_Server
service ftp
action source-nat address-group "DMZ pool"
#
quota-policy
#
pcp-policy
#
dns-transparent-policy
#
rightm-policy
#
return
123456789101112131415161718192021222324252627282930313233343536373839404142434445464748495051525354555657585960616263646566676869707172737475767778798081828384858687888990919293949596979899100101102103104105106107108109110111112113114115116117118119120121122123124125126127128129130131132133134135136137138139140141142143144145146147148149150151152153154155156157158159160161162163164165166167168169170171172173174175176177178179180181182183184185186187188189190191192193194195196197198199200201202203204205206207208209210211212213214215216217218219220221222223224<\:fm\\"=admhabcl@%@%>
- R1
显示R1配置
1
interface GigabitEthernet0/0/0
ip address 1.1.1.2 255.255.255.0
#
interface GigabitEthernet0/0/1
ip address 12.1.1.1 255.255.255.0
#
interface GigabitEthernet0/0/2
#
interface NULL0
#
ospf 1 router-id 1.1.1.1
area 0.0.0.0
network 12.1.1.1 0.0.0.0
#
1234567891011121314
- R2
显示R2配置
1
#
interface GigabitEthernet0/0/0
#
interface GigabitEthernet0/0/1
ip address 12.1.1.2 255.255.255.0
#
interface GigabitEthernet0/0/2
#
interface NULL0
#
ospf 1 router-id 2.2.2.2
area 0.0.0.0
network 12.1.1.2 0.0.0.0
#
……